Computers Physically Isolated From Public Network’s Can Still Be Hacked By Cell Phones

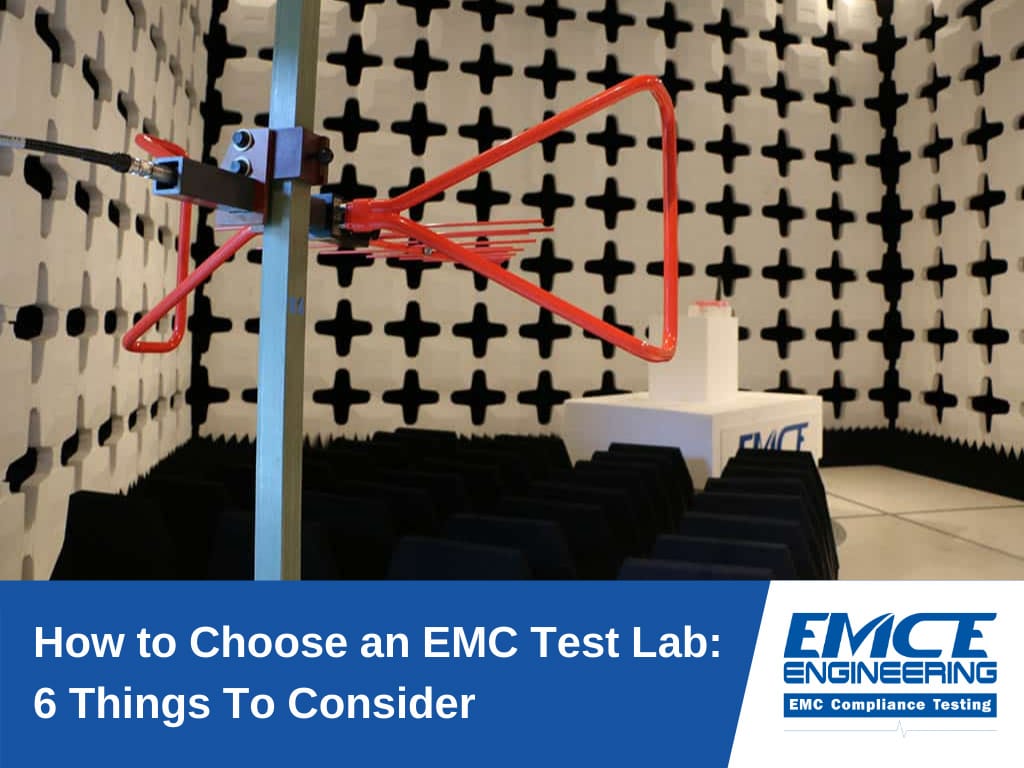
Air-gapped computers are isolated from public networks, physically and technically, to prevent hacking over the internet, but if the computers are not enclosed in Faraday Rooms to block RF emissions, they may not be safe enough.
Basic Security measures such as restricting the use of cell phones, limiting cell phone capabilities like cameras, video, and Wi-Fi features, may not be enough to stop this newly discovered threat.
Ben Gurion University of the Negev researchers, as part of the BGU Cyber Security Research Center, have recently discovered a threat to “secure” air-gapped computers. This is the third threat the BGU cyber team has uncovered related to air-gapped computers. “Whisper” demonstrated a covert bi-directional communication channel between two close-by air-gapped computers that used heat to communicate. “Air Hopper” was another method they discovered that utilizes FM waves for data exfiltration.
The research team has discovered how to use software that modifies the CPU firmware and uses the air-gapped computer as a cellular transmitting antenna. GSMem malicious software uses electromagnetic waves from cell phones to receive and infiltrate small bits of data, like password security keys and codes, and with a small footprint, it can be difficult to detect.
With an additional receiver, the distance for infiltrating data was successful as far away as 90 feet from the computer. Because computers emit electromagnetic radiation (EMR) an opportunity persistently exists because cellphones can easily receive these waves.
Countermeasures include increasing the size of the zone where mobile phones and devices are prohibited, insulating partition walls, anomaly detection, and behavioral dynamic analysis may all help prevent cell phone hacking even if the mobile device has been infected with a malicious code.
Article: “Amy Jones | HCTA”
Editor: “M. Danmole”
Image: “Security Affairs | Global EMC”